MARS SLCDR
SecuLetter Contents Disarm & Reconstruction
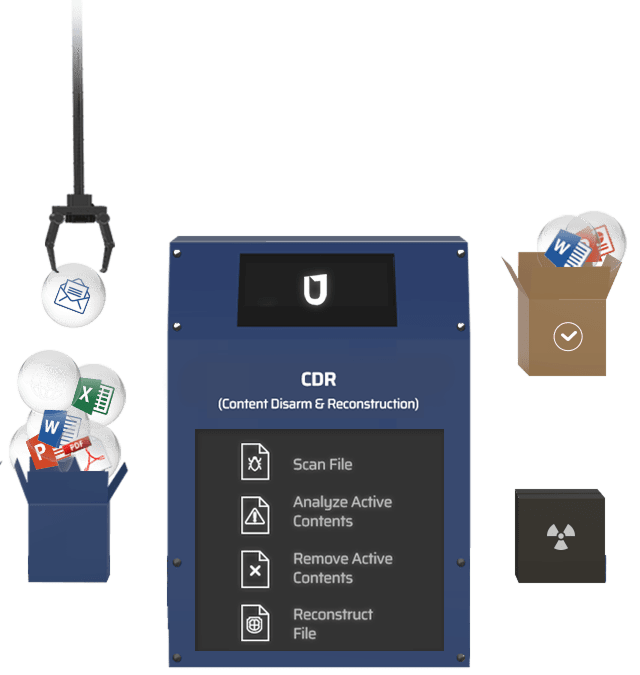
It removes hidden threats within files and reconstructs them to provide a Zero-Trust–based secure environment for using non-executable files.
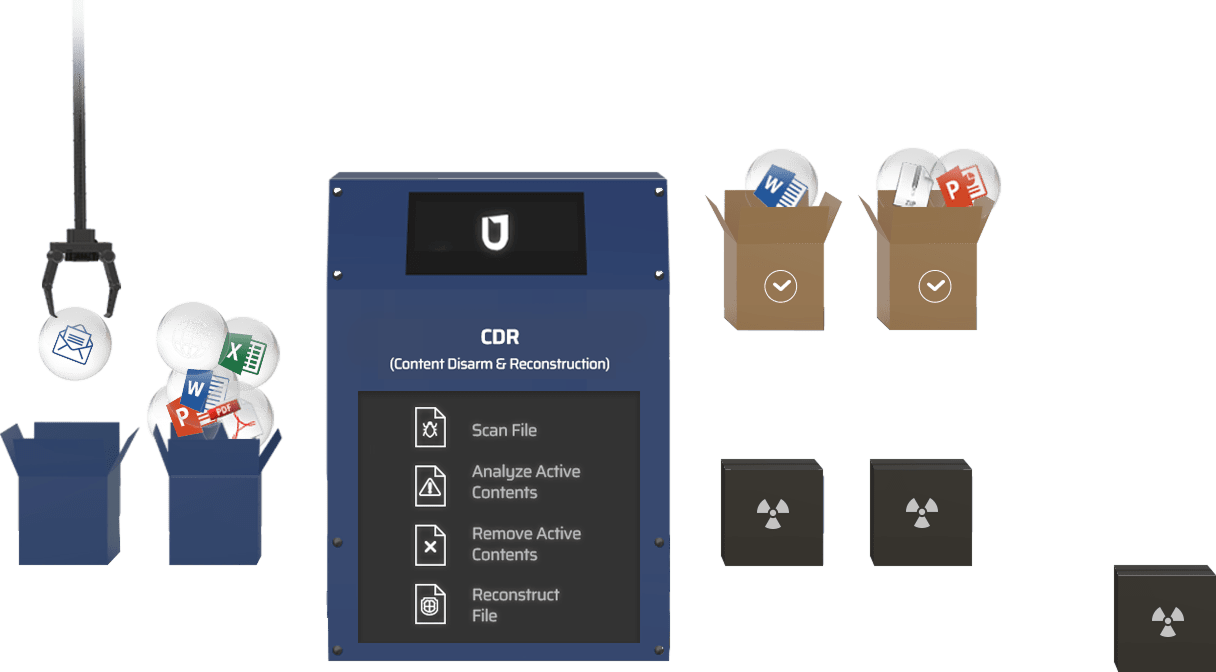
CDR
(Content Disarm & Reconstruction )
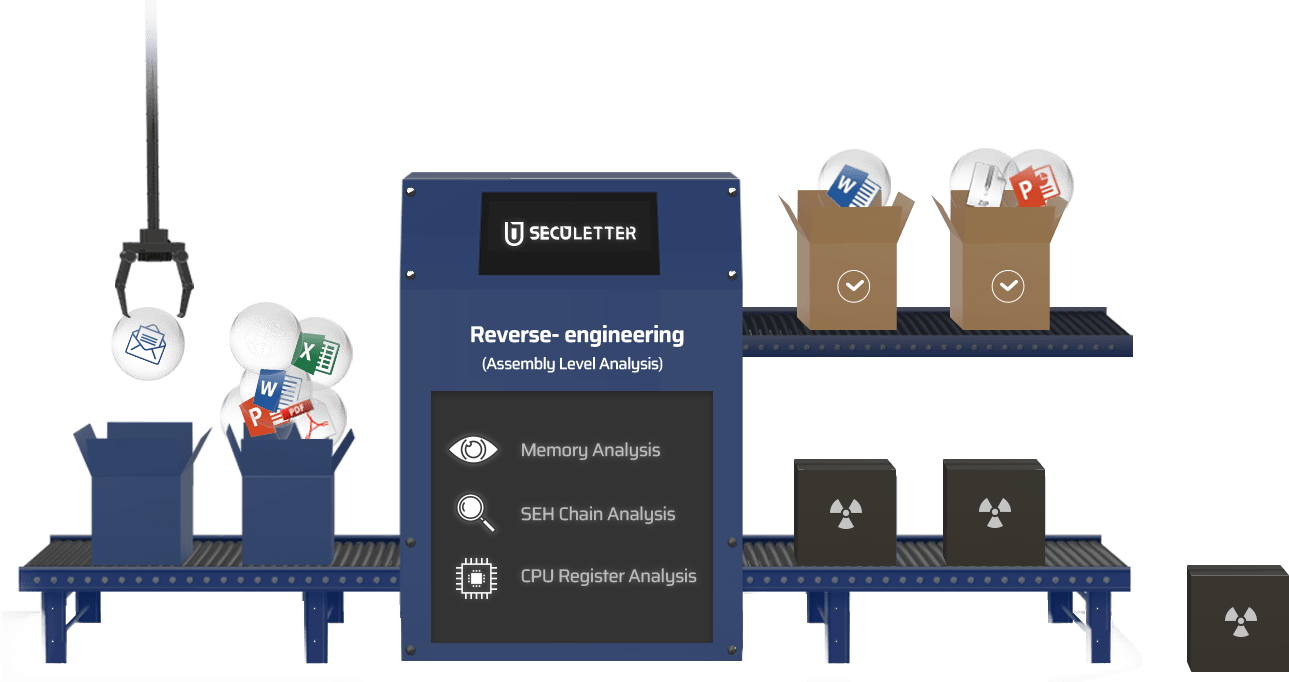
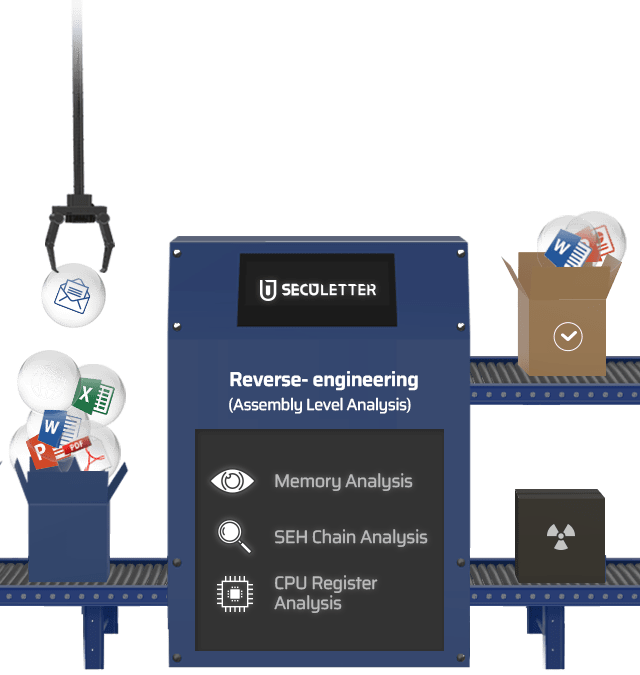
Content Disarm & Reconstruction (CDR) : Scan File → Analyze Active Contents → Remove Active Contents → Reconstruct File


Product Lineup
(On-Premises)
[On-Premises] MARS SLCDR: Optimized for fast performance and convenient operation in security environments such as network separation (inter-network linkage), integration with document centralization solutions, or file upload sections (e.g., web bulletin boards).
01
Zero-Trust–based email security environment
02
Supports a wide range of non-executable file types – MS Office, PDF, HWP, images, videos, text, EML, MSG, OneNote, etc.
03
Removal-based approach instead of detection-based, eliminating the need for event response and enabling convenient operations
04
Supports disarming of embedded documents within a file
05
Patented active content removal method that preserves the document format closest to the original
06
Integration with file systems via SMB, NFS, SSH (SFTP) protocol support
Key Features
Based on differentiated document analysis technology, it provides a Zero-Trust–based document security environment through active content removal and document reconstruction.

Document Structure Analysis Technology
- Analyzes the validity of each document file type structure (MS Office, Hancom Office, PDF, images, etc.).
- Supports analysis of the latest versions of each document type.

Active Content Identification Technology
- Identifies active content embedded in documents (Hyperlink, DDE, Macro, JavaScript, OLE Object, etc.).
- Analyzes document layers to disarm (neutralize) embedded documents (OLE, embedded files, etc.) rather than simply deleting them.
- Determines the scope of active content removal and performs actions (retain as exception, remove) according to policy.

File Reconstruction Technology
- During active content disarm, only specific elements are neutralized instead of reconstructing the entire file, minimizing document modifications.
- Depending on the user’s operating environment, disarmed files can be converted into alternate formats during reconstruction (e.g., XLSM → XLS).
How It Works
Effectively addresses security threats associated with file sharing and boosts enterprise productivity.
- Network Separation Linkage
- Web Bulletin Board
- Document Centralization Solution
(External Network)
within documents, and finally reconstructs them into safe files free of active content.
SECULETTER AI, providing a higher detection rate compared to conventional IT systems.
(External Network)
(Internal Network)
(Internal Network)
within documents, and finally reconstructs them into safe files free of active content.
Intelligence
SECULETTER AI, providing a higher detection rate compared to conventional IT systems.
within documents, and finally reconstructs them into safe files free of active content.
Intelligence
SECULETTER AI, providing a higher detection rate compared to conventional IT systems.
within documents, and finally reconstructs them into safe files free of active content.
SECULETTER AI, providing a higher detection rate compared to conventional IT systems.
within documents, and finally reconstructs them into safe files free of active content.
SECULETTER AI, providing a higher detection rate compared to conventional IT systems.
within documents, and finally reconstructs them into safe files free of active content.
Intelligence
SECULETTER AI, providing a higher detection rate compared to conventional IT systems.
Case Studies
SecuLetter's MARS SLF is the ultimate solution for safeguarding your organization's digital assets.
University
The university turned their lectures into online class since COVID-19 occurred.
The students were asked to submit their assessments via student portal.
The IT security team concerned the possibilities of inflowing malicious code contained files
among those assessments. The IT security team tested multiple PoC and decided to adopt
SLF as it showed no latency of uploading files under busy traffic conditions.
Since the university adopted SLF, there were more than 1,000 files found that containing
malware.
Finance Company
The company needed to enhance the security environment as APT attacks using Non-PE files have been growing rapidly recently. After carrying out PoC of many APT solutions, the company eventually decided to adopt SecuLetter's SLF. During PoC, SLF showed great performance result with high detection rate & the fastest diagnose speed.
SLF supports API to integrate with existing 3rd party's solutions. The company uses
SLF with their enterprise security management system.
Public Insurance Company
SLF is integrated with WAS, and blocks 99.9% of malware threat. And also SLF's performance is 5 times faster than other solutions, so there is no latency in work performance.
See the Reality
Try SLE and see how many malicious emails your business receives everyday.
